Get a deep understanding of your players
Unify your player data in real time and deliver personalised campaigns that convert.
Trusted by top brands and partners









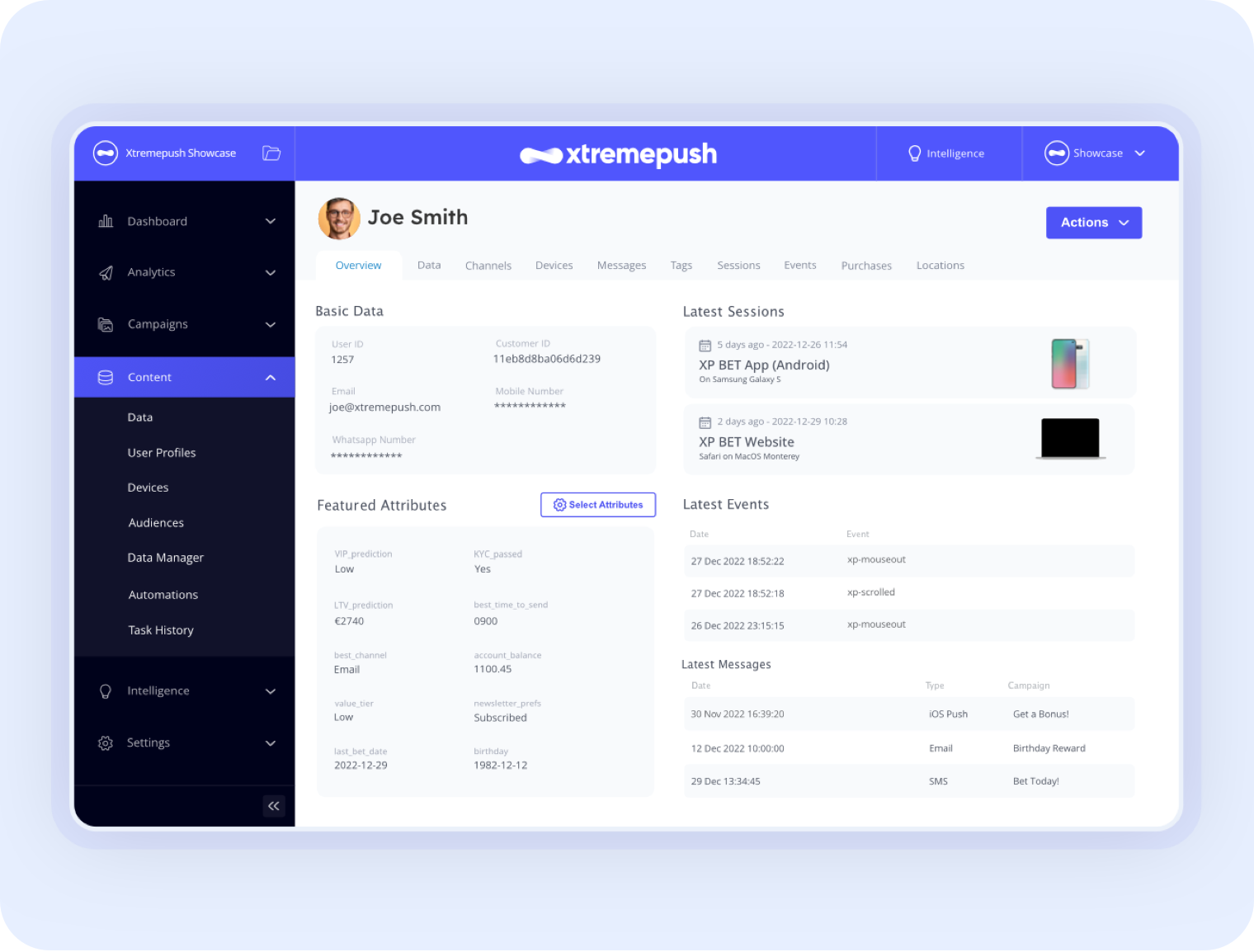
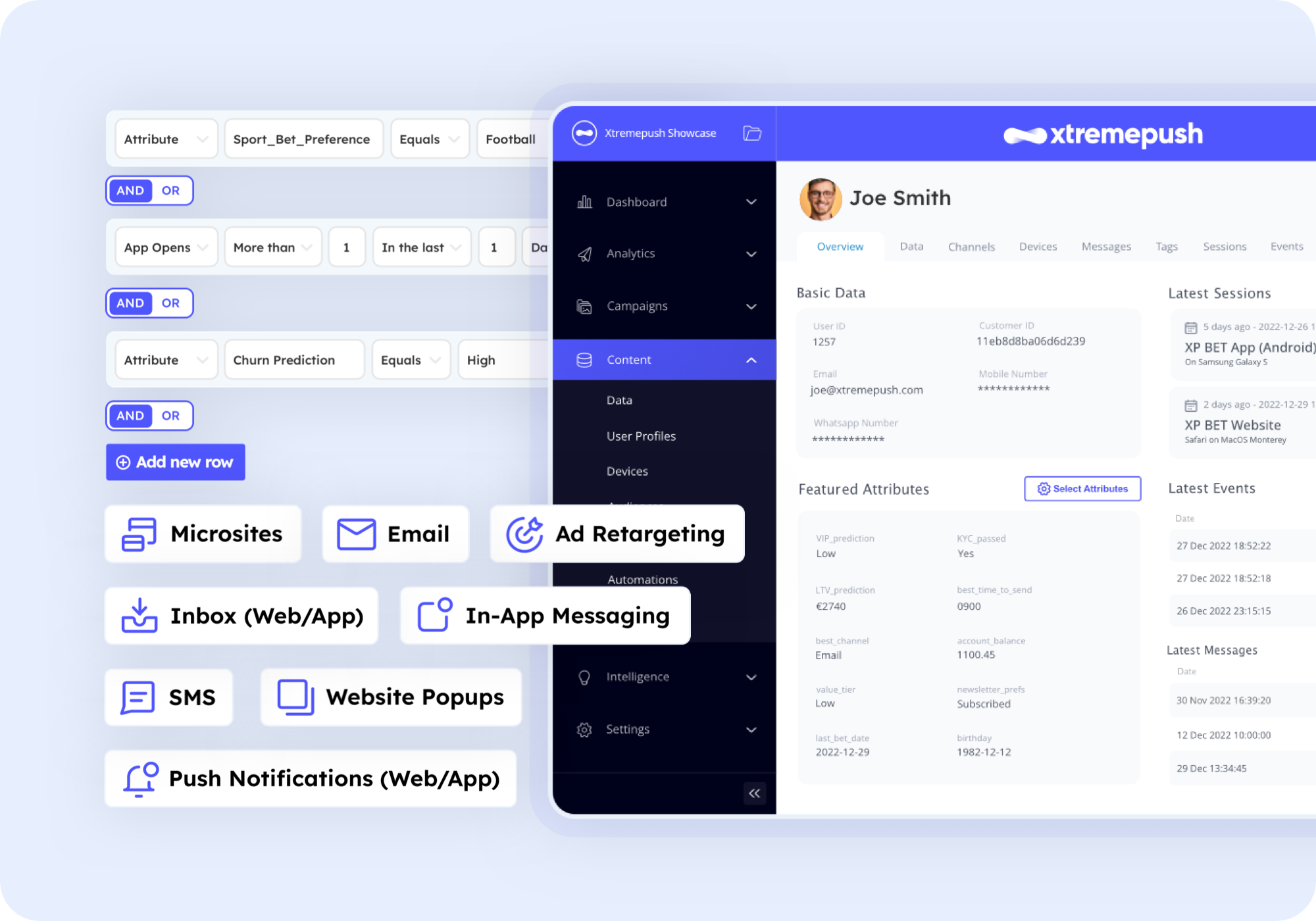
Single Customer View
Get a holistic view of your players
Collect and consolidate data from all sources and devices in real time and get a complete understanding of your players across all touchpoints.
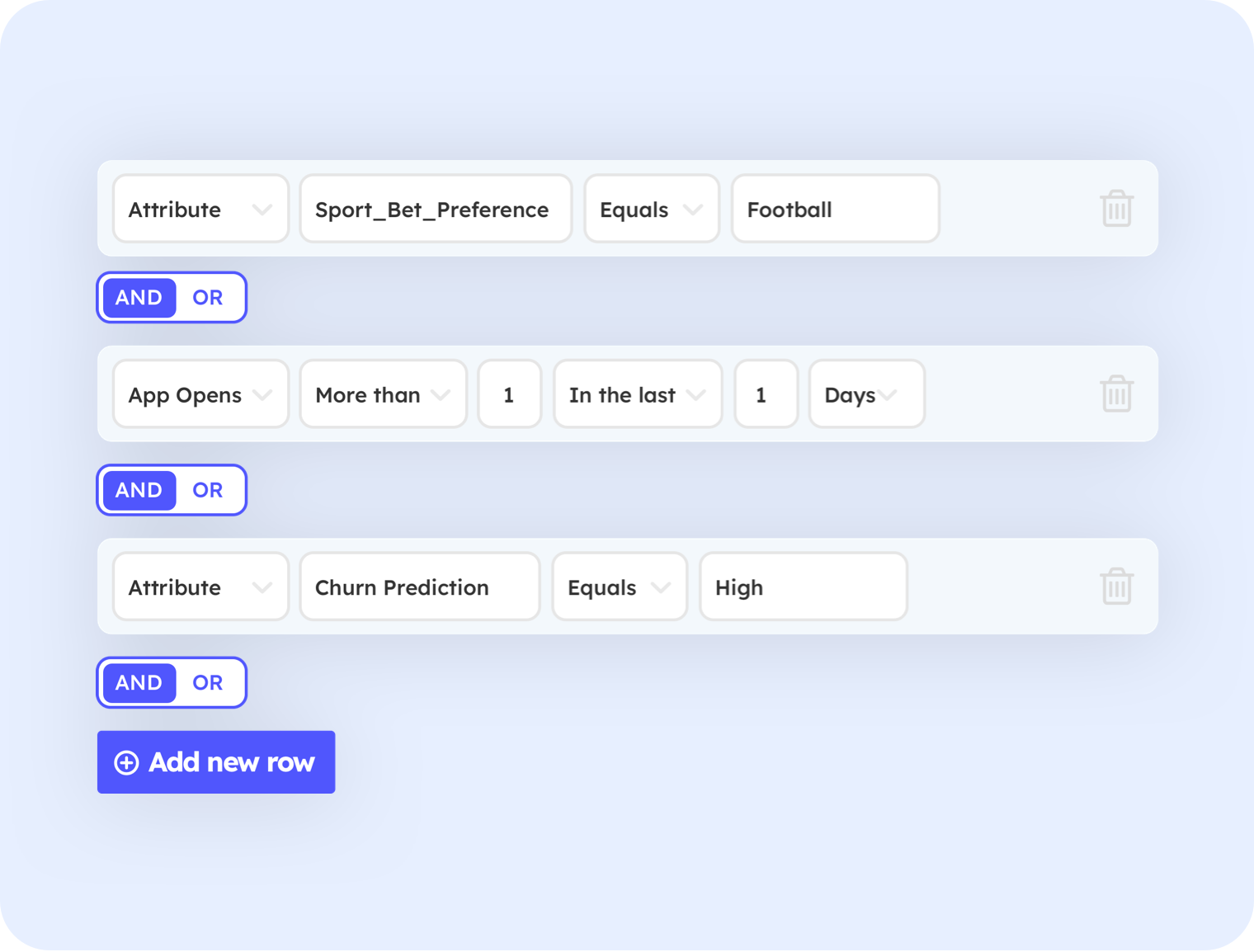
Dynamic Segmentation
Easily segment your players for one-to-one targeting
Build granular audiences based on historical, real-time, or predicted player behaviour to deliver highly relevant engaging communication that’s difficult to resist.
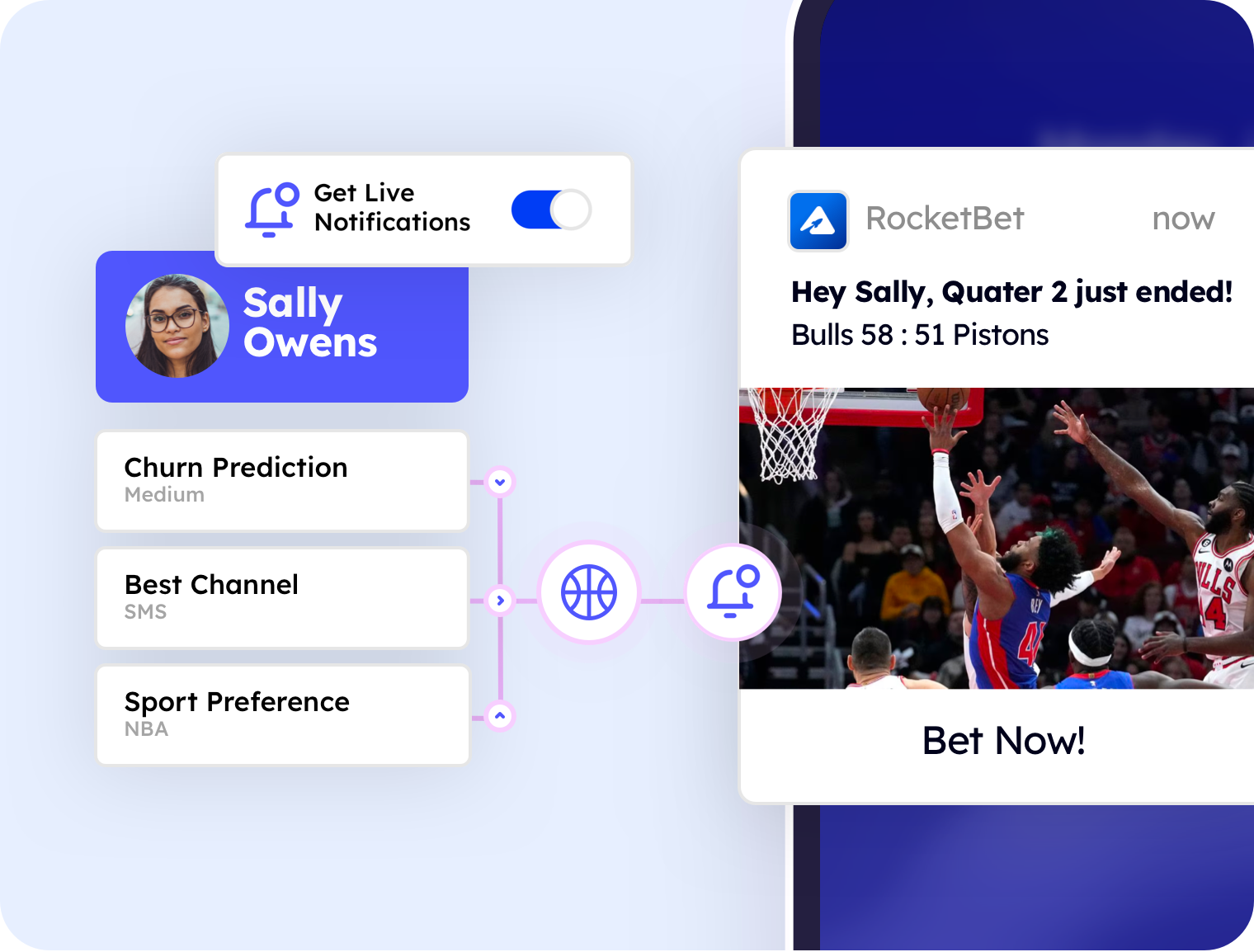
Behavioural Triggering
Never miss the right moment to engage your players
Target your players with personalised campaigns, triggered by historical, real-time or predicted behaviour to increase conversion and drive retention.
.png)
Omnichannel Activation
Deliver connected player experiences across all channels
Thanks to the unified nature of our platform, you can immediately use your unified player data to deliver personalised campaigns through our built-in channels.
.svg)
600%
Increase in average annual revenue
“By creating an experience that is unique and relevant to every player, our retention rate has been incredibly strong. In turn, this has also led to a 600% increase in our Average Annual Revenue which is a huge achievement for us.”

Andreia Oliveira
COO, Betsul
G2 reviews
.svg)
.svg)
.svg)
.svg)
.svg)
"Great product, support and results!"
.svg)
.svg)
.svg)
.svg)
.svg)
"Xtremepush is a game changer"
.svg)
.svg)
.svg)
.svg)
.svg)
"Really great platform for CRM Marketers"
Real-time CDP FAQ
-
How does the Real-time CDP ensure the security and privacy of customer data?
Xtremepush’ Real-Time CDP prioritizes data security and customer privacy at every step. We employ advanced encryption and compliance with global data protection regulations to safeguard unknown customer data and sensitive information. These robust security measures ensure that your customer's preferences and personal details are protected.
customer trust and maintaining the integrity of your customer relationship management. -
Can the platform integrate offline channels into the customer journey analytics?
Absolutely! Xtremepush is designed to unify customer data from both online and offline channels, offering a comprehensive view of the customer journey. Through integrating offline channels, such as in-store interactions and call center data, we provide a more complete picture of customer behaviour and preferences. The integration of these systems is fundamental to delivering personalised customer experiences and making informed decisions.
-
How does the Real-Time CDP utilise AI and machine learning for customer engagement?
Xtremepush leverages AI-driven insights and machine learning algorithms to analyse customer behaviour and predict future trends. All for creating more effective marketing campaigns and personalised interactions at incredible speed. The AI tools in our solution help you tailor your approach to engage and convert high-value customers.
-
What capabilities does the platform offer for managing and activating real-time customer data across multiple channels?
Xtremepush excels in collecting and activating real-time customer data across multiple channels. With features like streaming data collection and tag management, you can collect data and activate customer data seamlessly. This allows for the delivery of personalised experiences across various touchpoints, ensuring consistent and engaging customer service interactions.
-
How does the platform assist in breaking down data silos and enhancing digital transformation?
Xtremepush is designed to break down data silos by consolidating and unifying customer data from disparate sources. This unified approach is essential for effective customer data management and plays a pivotal role in digital transformation strategies. With a single view of the customer provided, our platform facilitates smoother analysis processes and more coherent customer experience management.
Ready to Grow With Us?
Take the first step to start your personalisation and omnichannel journey. Get in touch today!









